Need your computer fixed?
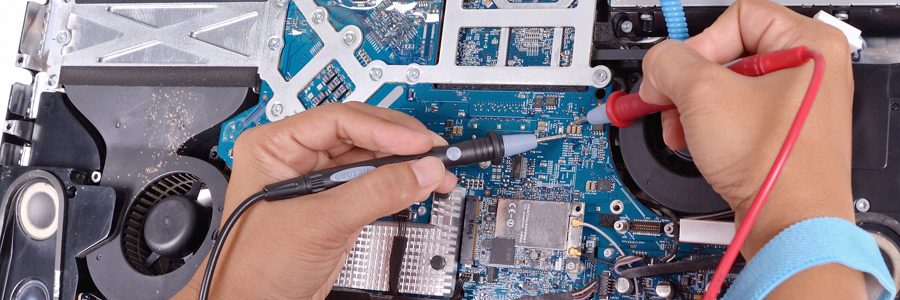
You’ll have a working computer because of Dave’s experience, tools and team of technicians. At your place or ours – we can help.
DoctorDave has been doing computer repair in Lawrence, Topeka and Kansas City since 1990. Whether it’s a computer crashing or locking up, nasty viruses and malware, or just a slow computer, DoctorDave can fix it!
Apple Macintosh or Windows PC: your computer will be fixed right away, and fixed correctly the first time. Desktop or laptop, hardware or software. We work on it all. You rely on your computer and you can rely on us.
Uniquely, we’ll tell you when it isn’t worth fixing so you don’t waste your money.
Dave’s team of trustworthy technicians go through a rigorous interview process including extensive background checks and training before they ever touch a computer. Our team has a combined experience of over fifty years.
We’re patient and punctual and get it fixed. Right. The first time.
Don’t take our word for it, read what our clients say about us.